Cybersecurity Blog
Thought leadership. Threat analysis. Cybersecurity news and alerts.
WannaCry Ransomware Infects Over 126,000 Computers in 104 Countries
More than 126,000 computers in 104 countries have been infected by the ransomware called “WannaCry”, this according to cybersecurity firm Avast. These latest ransomware attacks appear to be the biggest ransomware assault on the record.
WannaCry Victims
In the UK, the WannaCry ransomware, which affected 16 medical institutions of the National Health Service (NHS), prevented doctors from accessing patient files and caused emergency rooms to divert patients. British Prime Minister Theresa May, while on the campaign trail said, "We are aware that a number of NHS organizations have reported they have suffered from a ransomware attack." The British Prime Minister added, "This is not targeted at the NHS. It is an international attack. A number of countries and organizations have been affected."
The attacks also spread to Russia. Russian Interior Ministry’s Spokeswoman Irina Volk told the Russian News Agency TASS that the ransomware attacked the computers of the Russian Interior Ministry. "As of now the virus has been localized. There have been no inside information leaks from the Russian Interior Ministry’s information resources," Volk said. In Spain, CCN-CERT – Spain’s Computer Emergency Response Team – posted a security alert on its site about the ransomware attacks that affected several Spanish organizations. Avast reported that WannaCry ransomware mainly targeted Russia, Ukraine and Taiwan. Cybersecurity firm Kaspersky Lab reported that it recorded over 45,000 attacks of the WannaCry ransomware in 74 countries around the world. Kaspersky said that the actual numbers of those affected could be higher. “It’s important to note that our visibility may be limited and incomplete and the range of targets and victims is likely much, much higher,” Kaspersky said. How WannaCry Ransomware Infected Computers Worldwide and How It Was Accidentally Stopped
Once a computer is infected by WannaCry, a bright red dialog box appears on the computer monitor with the notice: "Ooops, your files have been encrypted!" This dialog box clarifies that the infected computer’s documents, photos, videos, databases and other files cannot be accessed as they have been encrypted. The dialog box specifies that a victim may recover his or her files by paying a US$300 ransom to be paid in bitcoin. The dialog box also shows that the US$300 ransom payment will be doubled after three days, and if no payment is made after seven days, the encrypted files will be deleted. In addition to the dialog box, the ransomware also changes the infected computer’s wallpaper with a notice on how to proceed with the ransom payment and decryption process. 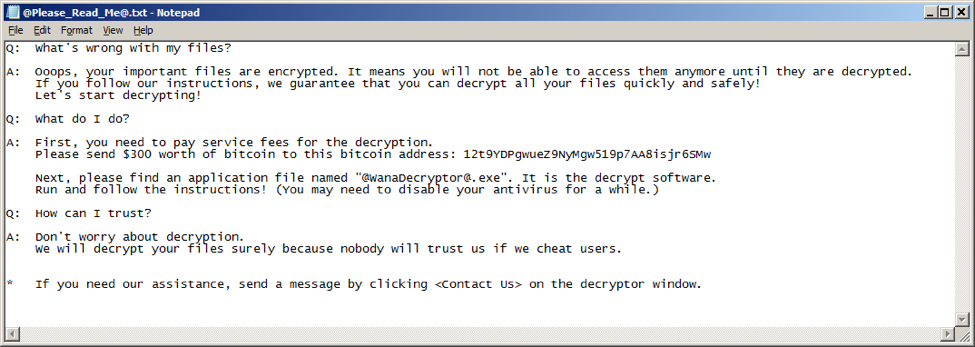
The ransomware also drops a text file to the computer with further instruction about the ransom payment and decryption process – an option for those who have closed out the dialog box, or those who have no idea what the dialog box is about.
Spain’s Computer Emergency Response Team CCN-CERT identified the latest ransomware as a variant of the ransomware known as WannaCry. This latest ransomware, CCN-CERT said, is spreading to other computers by exploiting a known remote code execution vulnerability in Microsoft Windows computers. Spain’s Computer Emergency Response Team CCN-CERT added that this malware has the ability to spread itself within corporate networks, without user interaction. “Infection of a single computer can end up compromising the entire corporate network,” CCN-CERT said. According to Avast, this specific vulnerability in Microsoft Windows was first exploited by Equation Group – a group widely suspected of doing the hacking activities of the National Security Agency (NSA). The hacker group known as ShadowBrokers, Avast said, stole from the Equation Group the hacking tool that exploits this particular vulnerability in Microsoft Windows. On April 14, 2017, ShadowBrokers published on the internet this specific vulnerability in Microsoft Windows and the hacking tool to exploit it – codename “EternalBlue”. On March 14, 2017, one month before Shadowbrokers made public EternalBlue, Microsoft issued a patch or security update. According to Microsoft, the March 14th patch resolves this specific vulnerability in Microsoft Windows. “The most severe of the vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server,” Microsoft said. With the extent of these latest ransomware attacks, it appears that many organizations around the world have not yet installed Microsoft’s March 14th patch. At the height of WannaCry attacks on May 12, 2017, Microsoft issued an update to customers who have not received the March 14th security update. “We also know that some of our customers are running versions of Windows that no longer receive mainstream support. That means those customers will not have received the above mentioned Security Update released in March. Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download …,” Microsoft said in a statement. The 22-year-old British researcher who goes by the name "MalwareTech" confirmed that he accidentally stopped WannaCry attacks. MalwareTech said that upon realizing that the kill switch’s domain name of WannaCry was not yet registered, he bought the domain name himself. The ransomware attack stopped spreading when the kill switch’s site bought by MalwareTech went live. How to Prevent Future Ransomware Attacks
To prevent WannaCry attacks, Spain’s Computer Emergency Response Team CCN-CERT recommends the following:
For its part, software company Symantec said that new ransomware variants appear on a regular basis. Symantec recommends the following best practices against ransomware:
We also recommend implementing preventative controls and blocking encrypted Word files from entering the networks via email. While document sharing and collaboration are important, sharing encrypted Word file via email may not be the best, and not the most secure collaboration solution. Solid detective controls must include ongoing vulnerability assessment and management, and we can help your organization to stay ahead of the pack protecting your most valuable digital assets. And finally, we highly recommend implementing a cybersecurity awareness program, including comprehensive employee training considering that it’s the first, and the most important line of defense against cyber crime. Your comment will be posted after it is approved.
Leave a Reply. |
AuthorSteve E. Driz, I.S.P., ITCP Archives
June 2024
Categories
All
|
5/14/2017
0 Comments