Cybersecurity Blog
Thought leadership. Threat analysis. Cybersecurity news and alerts.
How to improve healthcare cyber securityScope of Hacking Health Care Records
The hacking of health care records at the NHS and HPMC aren’t isolated cases. Prior to the widely published WannaCry ransomware attack, other cyber attacks had already wreaked havoc in the health care industry. Protenus reported that in 2016, the U.S. health care industry suffered one breach per day, affecting more than 27 million patient records.
For the month of April 2017 alone, the U.S. Department of Health and Human Services, Office for Civil Rights reported 12 hacking incidents on hospitals and medical doctors’ offices, affecting 171,564 patient records. The biggest hacking incident last month that was reported to the U.S. Department of Health and Human Services happened at Harrisburg Gastroenterology Health Care Center, affecting 93,323 patient records. The patient information potentially accessed at Harrisburg Gastroenterology includes names of patients, demographic information, social security numbers, health insurance information, diagnostic information and clinical information. Last May 18th, Neeley-Nemeth Barton Oaks Dental Group reported to the U.S. Department of Health and Human Services that its computer system was hacked, affecting 17,090 patient records. Symantec's Global Ransomware and Business Special Report showed that from January 2015 to April 2016, Canada ranked third (16%) in terms of ransomware infections, next only to the United States (23%) and "Other Regions" (19%). Verizon’s 2017 Data Breach Investigations Report showed that breaches in healthcare organizations came second (15%), next to data breaches in financial organizations (24%). In 2017, ransomware was ranked by Verizon as the number five most commonly used crimeware. “For the attacker, holding files for ransom is fast, low risk and easily monetizable – especially with Bitcoin to collect anonymous payment,” the Verizon report said. 5 Reasons Why Hacking of Health Care Records is Skyrocketing
Hospitals and medical doctors’ offices have become targets for ransomware attacks due to the following reasons:
1. Medical Records are Irreplaceable Medical doctors’ offices and hospitals have irreplaceable digital documents that increase every hour, from appointments with patients to viewing imaging. 2. Willingness to Pay Compared to other sectors, the medical sector appears to be more than willing to pay ransom for the fast recovery of their data. 3. Confidential Nature of the Documents Medical doctors’ offices and hospitals’ records carry with them an abundance of confidential information about patients such as social security details, insurance details, birth dates, addresses, medical history and current medical situation. These confidential data can be sold to other opportunistic individuals or organizations at $10 per patient – an amount 10 times higher than what criminals earn from selling credit card details. 4. Loss of Reputation Hacking exposes organizations their weakness. As such, many hospitals and medical doctors’ offices would rather pay and keep quiet than face the consequence of loss of reputation. 5. Vulnerable Software Many medical doctors’ offices and hospitals use proprietary software. Cyber criminals exploit the vulnerabilities of these proprietary software solutions. In the case of the NHS WannaCry ransomware attack, the vulnerability of the operating system Windows XP was exploited. At the height of the WannaCry attack, NHS confirmed that 4.7% of the organizations’ computers still use Windows XP – an operating system released by Microsoft in 2001. 3 Effective Ways to Prevent Cyber Attacks on Medical Doctors’ Offices
Below are 3 preventive measures to stop cyber criminals from getting hold of your patients’ confidential data:
1. Backup data One of the effective means to prevent cyber attacks, specifically ransomware attacks, is by backing up your data. Ransomware attackers have an advantage over their victims by encrypting valuable computer files and preventing victims to access these valuable files. If you’ve backup copies, it would be easy to bring back these files. It’s important to make sure that these backup files are properly protected. Storing them offline is one alternative so that cyber criminals can’t access them. Another option is to use cloud services. These cloud services keep previous versions of files, enabling you to roll back to the unencrypted form. 2. Exercise digital hygiene Preventing cyber attacks on medical doctors’ offices is similar to other disease prevention: hygiene is essential. In the medical office set-up, digital hygiene refers to maintaining one’s computer hardware and software solutions as secured as possible. Examples of digital hygiene include updating your hardware systems, installing the latest patches or software security updates, and not clicking unfamiliar links or files in emails. Hundreds of thousands, if not millions, of computers were unharmed by WannaCry ransomware by simply using the latest operating system and installing the latest patch or security update. 3. Contain the infection Containing a malware is much like containing an infectious disease outbreak. In such a case, a rapid response such as isolating the infected computers can make a difference. Many ransomwares like WannaCry have a worm component that’s capable of spreading itself within computer networks without the need for user interaction. In handling the WannaCry ransomware attack, Spain’s Computer Emergency Response Team CCN-CERT, for instance, recommended isolating from the network or turning off as appropriate computers without support or patch. Contact us today if you want to protect your hospital or medical office from cyber attacks. How to Create a Cyber Security CultureIn this world of frequent hacks and attempted hacks, it is more important than ever to foster a cyber security culture in your business. Unfortunately, this is easier said than done. Keep reading to learn more about how to create a cyber security culture among your employees. Remember the BasicsThere are a few basic cyber security measures that every business should be taking, including the following: Strong PasswordsIt seems simple, but a strong password is an important step in protecting against a cyber attack. Make sure that you and all your employees are using long passwords that include a mix of capital and lowercase letters, numbers, and special characters. Update Your Software RegularlyMost software has some glitches in it, no matter how long it's been on the market. While these glitches often aren't even noticeable, they can sometimes make you more vulnerable. Stay one step ahead of potential attackers and keep your software up to date. This is especially important for programs like antivirus scanners and your firewall. Limit AccessNot every employee needs access to every part of your computer network. Limiting access to sensitive data to only those who need to work with it is another simple way that you can create a cyber security culture in your workplace. With access limited, everything is not automatically made available to someone who hacks into one employee's account. Let Your Employees Know Why They Should Protect ThemselvesYou understand the importance of cyber security, but your employees might not. If your employees think your security policies are excessive or unnecessary, they aren't likely to follow them. Make sure you're teaching your employees the importance of cyber security. There are a few ways you can accomplish this: Help Them Find Their MotivationIt's important to find what motivates your employees to protect their information. Talk to them about potential security issues and the implications of a security breach. For example, do they want to protect their families and their personal finances? Making things more personal will help motivate employees to follow through with your cyber security measures. Discuss The Benefits Of Cyber SecurityIn addition to personal motivation, talk to your employees about how increased cyber security helps the company as a whole. Remind your staff that a lack of cyber security may reflect badly on your company. Your customers or clients want to know that their information is safe. They might take their business elsewhere if they think your employees and the company as a whole do not care about security. Keep It SimpleIt's important not to overload your employees with information. Rather than bombarding them with new programs and policies, start small and figure out which behaviors you want to promote first. Over time, as your employees get comfortable with initial security measures, you can take things a bit further. If they feel overwhelmed or frustrated by a deluge of information, employees are more likely to resist the changes. How Do You Create A Cyber Security Culture?What do you think of our list of tips for creating a cyber security culture? What other steps would you take? Let us know in the comments below! You can also contact us today to learn more about how to protect your business.
5 Signs You've Suffered An Online HackAre you unknowingly leaving your company's system vulnerable to external attacks? From a low of 18% in 2011, the number of online hacks targeting small businesses has risen to 43% in 2016. And this figure is expected to rise in the next couple of years. It's safe to say, therefore, that no business or industry is invincible when it comes to these malicious attacks. Figuring out if you've been a victim of an online hack or not is not so straightforward. But there are a couple of tell-tale signs which you can rely on when having doubts about the security status of your system. Let's dive right in. 1. A drop in website performanceIf keeping tabs on your website's technical performance is not part of the routine checks you carry out, it's about time you made it a priority. This is a proven way of picking up on slow or broken processes which could point to an online hack. For example, It should take an average of 4 seconds or less for a client to checkout of an e-commerce website. If it's taking longer than usual, this could point to a system breach. It's advisable to get a free vulnerability assessment just to be sure this is not a hacking attempt. 2. Does your antivirus appear disabled?If you notice your system's antivirus has been disabled without your knowledge or consent, this is a sign of a much bigger problem. When hackers infiltrate your system, you'll be unable to re-enable the antivirus. Disabling the antivirus is a common tactic used by hackers to maintain control and access to your system. 3. Server log activities you can't explain point to an online hackHave you noticed suspicious activity in your server and website logs lately? Keeping track of your server logs is an advanced way of detecting hackers trying to gain access to your system. Keep an eye out for these two common warning signs in your server logs:
4. Getting redirected online searches is a bad signSome hackers get paid if they can maliciously redirect internet searches to a different website without the user's knowledge. You'll end up getting blacklisted for unknowingly sending users to malware-infested sites. And that's not all. Users being re-directed to other sites means lost revenue for your business and damage to your reputation. 5. You can't explain the origin of new browser toolbarsThe main source of unwanted toolbars on your web browser is free online software which comes attached with ''crapware''. Simply put, crapware is a kind of software you don't need in your system and which gets installed against your will. Crapware is common in pre-installed programs or self-starting applications which alter your search engine settings. Pro tip: If you suspect your system has been compromised by an online hack, it's advisable to restore your system to the best-known state before proceeding with further safety measures. The current wave of cybercrime we're witnessing is worrying, to say the least. Security managers, therefore, need a more proactive approach to keep online hacks at bay. And being on the lookout for these signs is a step in the right direction. You can connect with us round the clock if you suspect your system has been hacked or is under attack. Keeping your online presence safe is our core business!
5 Cyber Security Threats To Look Out ForAs the world becomes more technological, so do the cyber criminals. From bank details to medical records, we store our most sensitive information on the web. Savvy swindlers take advantage of this new arena with a variety of scams designed to rob you of money, information, and identity. Protect your business by looking out for these common cyber security threats. Mobile transactionsDid your dad ever warn you about the danger of paying for things on the internet? Turns out his paranoia could be valid. A new host of vulnerabilities are available for fraudsters to exploit. They're hidden in the complexities of online payment platforms. Weak points are lurking in virtual wallets and CNP (card not present) transactions. Mobile transactions are predicted to exceed $220 billion in 2017, an enticing number for a scam-artist seeking a quick win. RansomwareHow could we forget the recent Wannacry ransomware attack While criminals promised to send the description keys to unlock your files, crime fighting cyber security experts released the keys free of charge. Ransomware is usually deployed to extort money, and it won't be changing any time soon. The hackers demand a ransom for locked personal or business information against the threat of deleting the precious data forever. On the flip side, vital information is 'kidnapped' until the victim pays for its release. These types of cyber security threats continue to increase. Avoiding suspicious links and downloads is an effective preventative against ransomware. DDoS attacksDistributed Denial of Service attacks are cyber security threats that aim to make a site useless. The hacker will infect and commandeer a network of connected devices. This "botnet" overloads the site with requests, preventing users from accessing the service. Hackers use DDoS to extort money, eliminate competition, or make a political statement. The increasing reliance on website traffic makes DDoS attacks devastating to modern businesses. IoT attacksThe Internet of Things heralds an age when your alarm clocks can instruct your coffee machine to turn on. This interconnectivity of devices can optimize your lifestyle. It can also make it vulnerable to cyber security threats. Hackers use IoT attacks to steal information, manipulate devices, and launch DDoS attacks. Phishing attacksMost people know the risks of opening unsolicited attachments and strange links. Phishing scams have had to up their game. These days it's harder to spot a phishing email. They're created with an intimate knowledge of the user, which entices them to click. The dodgy link opens the gateway to malware, which steals information. The phisher may also use your email to distribute phishing emails to your contacts list. How to defend against cyber security threatsWhile the face of cyber security threats is always changing, staying up-to-date on attack trends should be your first line of defense. Educate your staff on the appearance and symptoms of common cyber attacks. Common password hacks are among the simplest ways for scammers to access your system. Ensure your team practices healthy password hygiene and are vigilant about locking devices. The help of an information security specialist can help you to further fortify your systems and identify weaknesses before they become real threats. Contact us today and let's protect your business from cyber attacks.
How to Choose the Ideal Cyber Security CompanyLooking for a cyber security company? Protecting your business in not a luxury, it's a necessity. 2016 saw more cyber security breaches than any other year on record. In fact, according to the Identity Theft Resource Center (ITRC), 1,093 attacks occurred that year--up 40% from the year before. The ITRC reports that most of the data breaches were the result of email compromise schemes. The second most common type of breach was the result of accidental email or internet exposure of information--employee errors. Are You Protected?The Financial Post reports that about 36% of Canadian IT professionals know their companies have experienced a security breach. Many breaches go undetected and reporting them is critical to your company's future. These breaches can harm not only the business that's been attacked but the clients that are served by the businesses. An attack has many costs, and one of them is the trust a client puts in you--you may lose that trust and it'll cost you. Is your company putting its clients and customers at risk for identity theft? If your answer is maybe, read the easy guidelines below that will help you find a cyber security that will meet your company's needs. Finding the Right Cyber Security CompanyEnsure that the company you hire bases its work on the three pillars of cyber security: people, processes, and technology. PeopleWithin you company, everyone should receive proper training about how to avoid making your network vulnerable. At the company you hire, the employees should strive to keep up to date with the most current threats and the technology to thwart them. ProcessYour organization must have standards in place that operate as the rules for how to avoid a cyber attack. These standards should be managed by an information security management system that can be put in place by your own technicians or by the cyber security company you hire. TechnologyThe technology you employ must be up to date to counter current threats. This should include malware protection, secure mobile and web use for employees, network security, and secure configurations. Conflict of InterestEnsure that the firm you want to hire doesn't have a relationship with hardware or software companies that might keep them from having your best interests at heart. Hopefully, you can find a firm that has developed its own technology and isn't relying on someone else. Going along with the idea of having your best interests at heart, can the firm you're considering tailor their services to your business? Or do they only do one thing for everyone who hires them? Are They Insured?Did you know that cyber security companies should carry insurance just like any other contractor you hire? Who Else has Hired Them?Find out what other companies trust the firm you're considering. Are some private, some public? Are some commercial and some government? You want someone who has represented a variety of businesses so that you can benefit from what the firm has learned in dealing with a range of issues your own company may or may not encounter. In other words, you want the firm you hire to be prepared for anything that may come your way. What to doIf what you've read has come as news to you, consider finding help. Your business is on the line and the trust your clients and customers place in you is at stake. Act today.
Why North America is Behind in Cyber Security WorkforceIt does probably not come as a surprise to you, that there is a severe shortage in the cyber security workforce. Especially in North America. According to the Indeed Spotlight: The Global Cybersecurity Job Gap, the US is ranked 4th in the world for employer demand for cyber security talent. The Indeed article also tells us that specifically, network security specialists are in high demand. This is the skill set that is most desired by employers on a global level. Although this news may not be a surprise, you're probably asking yourself, why is it so. Why's there a Skills Gap in the Cyber security Workforce in North America?The why of the skills gap in the cyber sector dates back to why the internet was created in the first place. As stated in the Fraser Institute's Cybersecurity challenges for Canada and the United States, "The Internet was designed not with security in mind, but rather an openness and the free flow of information." Cybersecurity wasn't considered much until recent years. It wasn't until governments corporations, individuals, and the like became to realize the importance of protecting cyberspace. As so the challenge of how to protect the internet without hindering the freedom it represents was created. The reason North America is behind other countries when it comes to the cyber security workforce boils down to job seeker interest. Many employers are looking to hire those with advanced degrees and specializations in cyber security. And there are simply not enough of these employees to go around. Cyber security is not an easy job.Another reason for the gap in the cyber security industry is it's not a pleasant topic to think about. No one wants to discuss hacking, just as no one wants to discuss what happens in a case of a fire. It's one of those topics that no one does anything about because they don't think it's going to happen to them. Until it does. This brings to light two imperative topics all companies should consider, and they are The Importance of Cybersecurity Programs and Are the Biggest Cyber Security Risks your Employees. These two topics should no longer be avoided, as the trend for cyber criminal activity continues to rise. Companies need to stay up to date with all of their security measures. What can be done about the Cyber security Workforce Gap:A few options as expressed in a csoonline.com are:
In order to close the cyber security gap in the North American workforce, it's best to implement automated security solutions. This will help relieve the pressure until IT workers can be cross-trained or the interest in the sector picks up. Once the interest in the cyber security industry picks up it'll make it much easier to hire the appropriate staff.
How a Secure Website Can Boost Your SEOBack in 2014, Google announced that they would introduce HTTPS as a signal for ranking criteria. This was great news for anyone who had a secure website. However, there were questions. Was a secure website a good point for SEO, or was hardly a drop in the bucket? If it was a big deal, what type of certificates would help? There's a lot of questions, and unfortunately, not a lot in the way of answers. However, we're here to help provide some clarification. How does a secure website boost your ratings?Using a secure website as a ranking booster is still a relatively untapped way to jump up the Google ladder. Only about 2% of the top million websites redirect to a secure version of that site. This could be because there aren't that many websites that are secure. The main benefit to using a secure website is the fact that any user experiences will be secure. This is especially important if a user is transmitting data like credit card information. Of course, this should be obvious. It's not an up-and-coming cyber security precaution, but it does endure. You can see if your website is secure by looking at your address bar. If you see "https" before your URL, you're in the clear. Some browsers, such as Firefox and Google Chrome, highlight this in green to bring more attention to the fact. Security and SEO?The above may be true, but how does a site security help your website out in the important ranking race? Google has begun to prefer indexing secure versions of websites over insecure versions. For the most part, since so few people have made the switch to secure certificates, the use of a secure website acts as a tiebreaker in the race. For instance, if all other factors are dead on, neck-in-neck, the website which is secure will take precedence over the one that isn't. Your backups are safeThe great thing about using a secure website is that it doesn't erase your referrals or any of your data. You can switch over to a secure certificate and keep your referrals. Another plus? It almost guarantees that you'll keep your traffic. If your website and business relate to sales or other confidential information, it's almost mandatory that you use a security certificate. If you don't you risk your audience dropping off when they see that their information isn't secure. ConclusionA security certificate can be a lifesaver when it comes to your Google rankings. While there are still plenty of websites ranking without it, the idea of using a certificate is growing in popularity. In most situations, so few people have switched to using a certificate that it can't be factored into crucial criteria. However, a certificate can give you a leg up that can be used to break any ties between your site and another. In the ultra-competitive SEO world, you can take any advantages that you can get. For that reason, you'd be foolish if you didn't make the switch to using a security certificate. If you have questions regarding cyber security and how to keep your data safe, we're happy to get in touch with you and help you make your website secure.
5/15/2017 4 Tips for Better API Security4 Tips for Better API SecurityApplication Programming Interfaces (APIs) are everywhere, making life easier for consumers and companies on a global scale. Without API’s the digital economy would surely disintegrate. Thanks to API’s, sharing data between applications and legitimate developers has become easier than ever before. So has the risk of unintentionally sharing information with hackers. According to the Identity Theft Resource Center, there have been over 7000 network security breaches since 2005, involving 1000s of data records. A breach in your API security can have devastating effects on your business, damaging your reputation and your profits. These 4 security tips can help you save your business. 1. Be Vigilant from the StartFocus on your mobile app’s software security from the first line of code. Vulnerabilities in your source code could filter through to your API and beyond, especially in the case of native apps that are downloaded to the client’s device. Test and re-test your app code for weaknesses before putting it out there. Then protect it with the best encryption you can find and back that up with API encryption. Keep the client’s needs in mind. Don’t compromise on performance and user experience with heavy-handed security measures. 2. Make SSL/TLS the Rule for All APIsSecure network connections at the back end are vital. All servers and cloud servers that are accessing an app’s APIs should have security in place to guard against unauthorized data access. SSL/TLS are the building blocks of secure systems – use them, everywhere. Plus, you get the added SEO benefits that Google dishes out to SSL sites. SSL is your most effective protection against man-in-the-middle attacks. Add a VPN to that and you should be okay. Conduct a vulnerability assessment of your network to reveal weaknesses in your data protection methods. 3. Install Meticulous Identification, Authentication and Authorization ProceduresYour first line of defense in protecting your data is a gatekeeper to separate friend from foe. The use of identification, authentication and authorization technology will do just that and is vital for your legitimate users to prove who they are when accessing your app. OAuth2 has become the leading protocol for API security by managing connections securely with one-time tokens. You can configure and customize this framework to suit your needs. Likewise, OpenID Connect is a made-for-mobile protocol that assigns an ID token to your users, eliminating the need for cross-questioning them more than once with repeated sign-ins. 4. Don’t DIY When it Comes to API SecuritySave yourself the risk, expense, and effort of creating your own API security structure. Excellent security systems already exist for API’s - learn to use them. Putting your security systems in the hands of an expert is often the safest bet. Especially when it comes to protecting yours and your client’s sensitive data. API security cannot be overemphasized, make yours a priority so that you too can reap the benefits of modern technology to the best advantage. Talk to us, we can help you today.
WannaCry Ransomware Infects Over 126,000 Computers in 104 Countries
More than 126,000 computers in 104 countries have been infected by the ransomware called “WannaCry”, this according to cybersecurity firm Avast. These latest ransomware attacks appear to be the biggest ransomware assault on the record.
WannaCry Victims
In the UK, the WannaCry ransomware, which affected 16 medical institutions of the National Health Service (NHS), prevented doctors from accessing patient files and caused emergency rooms to divert patients. British Prime Minister Theresa May, while on the campaign trail said, "We are aware that a number of NHS organizations have reported they have suffered from a ransomware attack." The British Prime Minister added, "This is not targeted at the NHS. It is an international attack. A number of countries and organizations have been affected."
The attacks also spread to Russia. Russian Interior Ministry’s Spokeswoman Irina Volk told the Russian News Agency TASS that the ransomware attacked the computers of the Russian Interior Ministry. "As of now the virus has been localized. There have been no inside information leaks from the Russian Interior Ministry’s information resources," Volk said. In Spain, CCN-CERT – Spain’s Computer Emergency Response Team – posted a security alert on its site about the ransomware attacks that affected several Spanish organizations. Avast reported that WannaCry ransomware mainly targeted Russia, Ukraine and Taiwan. Cybersecurity firm Kaspersky Lab reported that it recorded over 45,000 attacks of the WannaCry ransomware in 74 countries around the world. Kaspersky said that the actual numbers of those affected could be higher. “It’s important to note that our visibility may be limited and incomplete and the range of targets and victims is likely much, much higher,” Kaspersky said. How WannaCry Ransomware Infected Computers Worldwide and How It Was Accidentally Stopped
Once a computer is infected by WannaCry, a bright red dialog box appears on the computer monitor with the notice: "Ooops, your files have been encrypted!" This dialog box clarifies that the infected computer’s documents, photos, videos, databases and other files cannot be accessed as they have been encrypted. The dialog box specifies that a victim may recover his or her files by paying a US$300 ransom to be paid in bitcoin. The dialog box also shows that the US$300 ransom payment will be doubled after three days, and if no payment is made after seven days, the encrypted files will be deleted. In addition to the dialog box, the ransomware also changes the infected computer’s wallpaper with a notice on how to proceed with the ransom payment and decryption process. 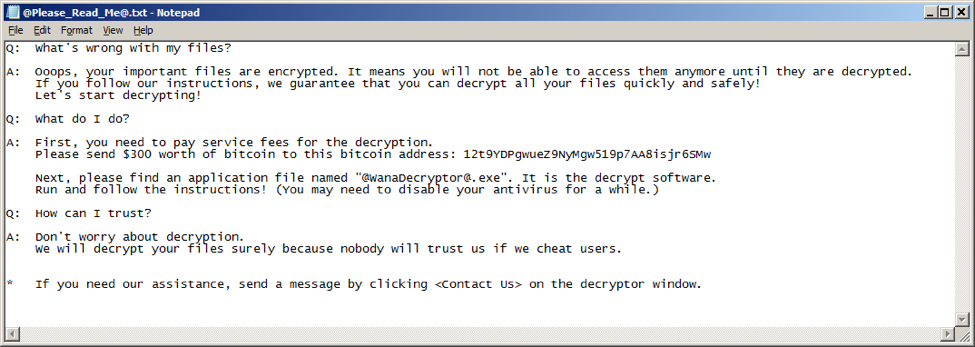
The ransomware also drops a text file to the computer with further instruction about the ransom payment and decryption process – an option for those who have closed out the dialog box, or those who have no idea what the dialog box is about.
Spain’s Computer Emergency Response Team CCN-CERT identified the latest ransomware as a variant of the ransomware known as WannaCry. This latest ransomware, CCN-CERT said, is spreading to other computers by exploiting a known remote code execution vulnerability in Microsoft Windows computers. Spain’s Computer Emergency Response Team CCN-CERT added that this malware has the ability to spread itself within corporate networks, without user interaction. “Infection of a single computer can end up compromising the entire corporate network,” CCN-CERT said. According to Avast, this specific vulnerability in Microsoft Windows was first exploited by Equation Group – a group widely suspected of doing the hacking activities of the National Security Agency (NSA). The hacker group known as ShadowBrokers, Avast said, stole from the Equation Group the hacking tool that exploits this particular vulnerability in Microsoft Windows. On April 14, 2017, ShadowBrokers published on the internet this specific vulnerability in Microsoft Windows and the hacking tool to exploit it – codename “EternalBlue”. On March 14, 2017, one month before Shadowbrokers made public EternalBlue, Microsoft issued a patch or security update. According to Microsoft, the March 14th patch resolves this specific vulnerability in Microsoft Windows. “The most severe of the vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server,” Microsoft said. With the extent of these latest ransomware attacks, it appears that many organizations around the world have not yet installed Microsoft’s March 14th patch. At the height of WannaCry attacks on May 12, 2017, Microsoft issued an update to customers who have not received the March 14th security update. “We also know that some of our customers are running versions of Windows that no longer receive mainstream support. That means those customers will not have received the above mentioned Security Update released in March. Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download …,” Microsoft said in a statement. The 22-year-old British researcher who goes by the name "MalwareTech" confirmed that he accidentally stopped WannaCry attacks. MalwareTech said that upon realizing that the kill switch’s domain name of WannaCry was not yet registered, he bought the domain name himself. The ransomware attack stopped spreading when the kill switch’s site bought by MalwareTech went live. How to Prevent Future Ransomware Attacks
To prevent WannaCry attacks, Spain’s Computer Emergency Response Team CCN-CERT recommends the following:
For its part, software company Symantec said that new ransomware variants appear on a regular basis. Symantec recommends the following best practices against ransomware:
We also recommend implementing preventative controls and blocking encrypted Word files from entering the networks via email. While document sharing and collaboration are important, sharing encrypted Word file via email may not be the best, and not the most secure collaboration solution. Solid detective controls must include ongoing vulnerability assessment and management, and we can help your organization to stay ahead of the pack protecting your most valuable digital assets. And finally, we highly recommend implementing a cybersecurity awareness program, including comprehensive employee training considering that it’s the first, and the most important line of defense against cyber crime. The Importance of Continuous Vulnerability Assessment and ManagementCyber security breaches are not a passing trend and the potential threats caused by cyber criminals are real, and on the rise. Especially when taking into consideration the cyber security predictions of 2017. Because there is so much at risk in the face of solving a security vulnerability, there are just as many reasons as to why continuous vulnerability assessment and management is important. Read on to learn the reasons why it's a must-have for any business. According to welivesecurity, "When a new vulnerability is reported, it triggers a race against the clock between the various people involved." This creates quite a bit of stress and puts a heavy workload on the shoulders of the IT department. The fact is that when a vulnerability is uncovered it must be solved in a timely manner to decrease the opening for exposure. This usually means that IT resources are spent around the clock. Without previous assessment and management of vulnerabilities, you might go above your human resources budget creating another set of problems. Unexpected and increased manpower expenditures are not the only concern when it comes to ways a cyber-attack can cost your company money either. Having a Continuous Vulnerability Assessment in Place can Save your Company's ReputationBesides the reasons of time, money, and resources, something else to think about is your company's reputation. Customers do not feel confident trusting a company that cannot keep itself safe from hackers, which can lead to taking their business elsewhere or not using your products or services in the first place. When you market online you should also worry about the overall online reputation management (ORM)to protect your public image, and companies like Reputation Mart could help. Keep in mind that most if not all security breaches are publicized. So preventing any issues your company may have pertaining to cyber security will either be spread by word of mouth or in the news. If you aren't aware of the problems your company has, putting it at risk, you can't fix them. Therefore, you're essentially making your business and your customers a target for cyber criminals who are just waiting for an opportunity to strike. Keeping up with Technology is Important in Order to Stay Ahead of CybercriminalsTechnology is ever-changing and evolving and companies need to do the same with their security measures if they want to keep up. This is why Tripwire reminds organizations that "security is an ongoing process" and "companies should, therefore, strive towards continuous vulnerability scans to pick up on those constant changes." By implementing a vulnerability assessment that is automated and completed on a continuous basis, (it cannot be just a one-time thing as threats will continue evolving) you'll be able to see where your company is at risk and prioritize what needs to be taken care of first. As your company grows, automation becomes more important as it helps to keep your IT team efficient and ahead of any potential network security threats. As you can see, having a continuous vulnerability assessment and management process in place is imperative. Because it will keep your company and customers safe. It will not only prepare you for the future which in turn will save time, money, and valuable company resources, but it'll also help to protect the company's reputation.
Vulnerability Assessment must not be limited to cybersecurity and should include physical security to better understand and mitigate the risks. There are many security companies that can help your business including pollarissecurity.com
Prevention and preparation for any potential online security breach are the best things to have in this day and age. |
AuthorSteve E. Driz, I.S.P., ITCP Archives
March 2024
Categories
All
|
5/30/2017
0 Comments